Security Settings
Protect your RAD Repairs account and data with comprehensive security features including two-factor authentication, password policies, session management, and audit logging.
The Security Settings panel provides centralized control over authentication and access policies
Overview of Security Features
RAD Repairs provides multiple layers of security to protect your business data and customer information. The Security Settings panel allows administrators to configure:
- Two-Factor Authentication (2FA) - Add an extra layer of protection beyond passwords
- Password Policies - Enforce strong password requirements for all users
- Session Management - Control how long users stay logged in and manage active sessions
- Login Attempt Limits - Protect against brute-force attacks with automatic lockouts
- IP Restrictions - Limit access to specific IP addresses or ranges
- Audit Logging - Track all security-related events and user actions
Security Best Practice: We recommend enabling two-factor authentication for all administrator accounts and setting a strong password policy. These measures significantly reduce the risk of unauthorized access.
Two-Factor Authentication (2FA)
Two-factor authentication adds an additional security layer by requiring users to provide a second form of verification beyond their password. RAD Repairs supports authenticator app-based 2FA using TOTP (Time-based One-Time Passwords).
Enabling 2FA for Your Account
Individual users can enable 2FA for their own accounts through their profile settings.
Access Security Settings
Click on your profile avatar in the top-right corner and select "Security" from the dropdown menu.
Enable Two-Factor Authentication
Click the "Enable 2FA" button to begin the setup process.
Scan QR Code
Open your authenticator app (Google Authenticator, Authy, Microsoft Authenticator, etc.) and scan the displayed QR code.
Verify Setup
Enter the 6-digit code from your authenticator app to confirm the setup is working correctly.
Save Backup Codes
Download and securely store the backup codes. These can be used to access your account if you lose access to your authenticator app.
Enforcing 2FA for All Users
Administrators can require all users to enable two-factor authentication. When this setting is enabled:
- New users will be prompted to set up 2FA during their first login
- Existing users without 2FA will be required to enable it on their next login
- Users cannot access the application until 2FA is configured
- Administrators can view which users have 2FA enabled in the User Management panel
Important: Before enforcing 2FA for all users, ensure that all team members have access to an authenticator app on their mobile devices. Consider providing a transition period and training for users unfamiliar with 2FA.
Password Policies
Strong password policies help prevent unauthorized access to user accounts. Configure the following password requirements:
Minimum Length
Set the minimum number of characters required for passwords. We recommend a minimum of 12 characters for strong security.
| Setting | Recommended Value | Description |
|---|---|---|
| Minimum Length | 12 characters | The minimum number of characters a password must contain |
| Maximum Length | 128 characters | The maximum number of characters allowed (prevents DoS attacks) |
Complexity Requirements
Require passwords to include a mix of character types for increased security:
- Uppercase letters (A-Z) - Require at least one uppercase letter
- Lowercase letters (a-z) - Require at least one lowercase letter
- Numbers (0-9) - Require at least one numeric digit
- Special characters (!@#$%^&*) - Require at least one special character
Modern Security Guidance: Recent NIST guidelines suggest that password length is more important than complexity. Consider requiring longer passwords (16+ characters) rather than complex combinations that users may struggle to remember.
Expiration Settings
Configure password expiration to require users to change their passwords periodically:
| Setting | Options | Description |
|---|---|---|
| Password Expiration | Never / 30 / 60 / 90 / 180 days | How often users must change their passwords |
| Password History | 0-24 passwords | Number of previous passwords that cannot be reused |
| Expiration Warning | 3-14 days | Days before expiration to start warning users |
Session Management
Control user session behavior to balance security with user convenience:
Session Timeout Settings
- Idle Timeout - Automatically log out users after a period of inactivity (default: 30 minutes)
- Maximum Session Duration - Force logout after a maximum time, regardless of activity (default: 8 hours)
- Remember Me Duration - How long "Remember Me" sessions last (default: 30 days)
Active Session Controls
Administrators and users can view and manage active sessions:
- View all devices and locations where the account is currently logged in
- Terminate individual sessions remotely
- Force logout of all sessions except the current one
- View session history including login times and IP addresses
Login Attempt Limits
Protect against brute-force attacks by limiting failed login attempts:
| Setting | Default Value | Description |
|---|---|---|
| Maximum Failed Attempts | 5 attempts | Number of failed attempts before account lockout |
| Lockout Duration | 15 minutes | How long the account is locked after exceeding attempts |
| Lockout Reset Period | 1 hour | Time after which failed attempt count resets |
| CAPTCHA Threshold | 3 attempts | Show CAPTCHA after this many failed attempts |
Locked Out? If a user is locked out of their account, an administrator can manually unlock it from the User Management panel. Users can also use the "Forgot Password" feature if email-based recovery is enabled.
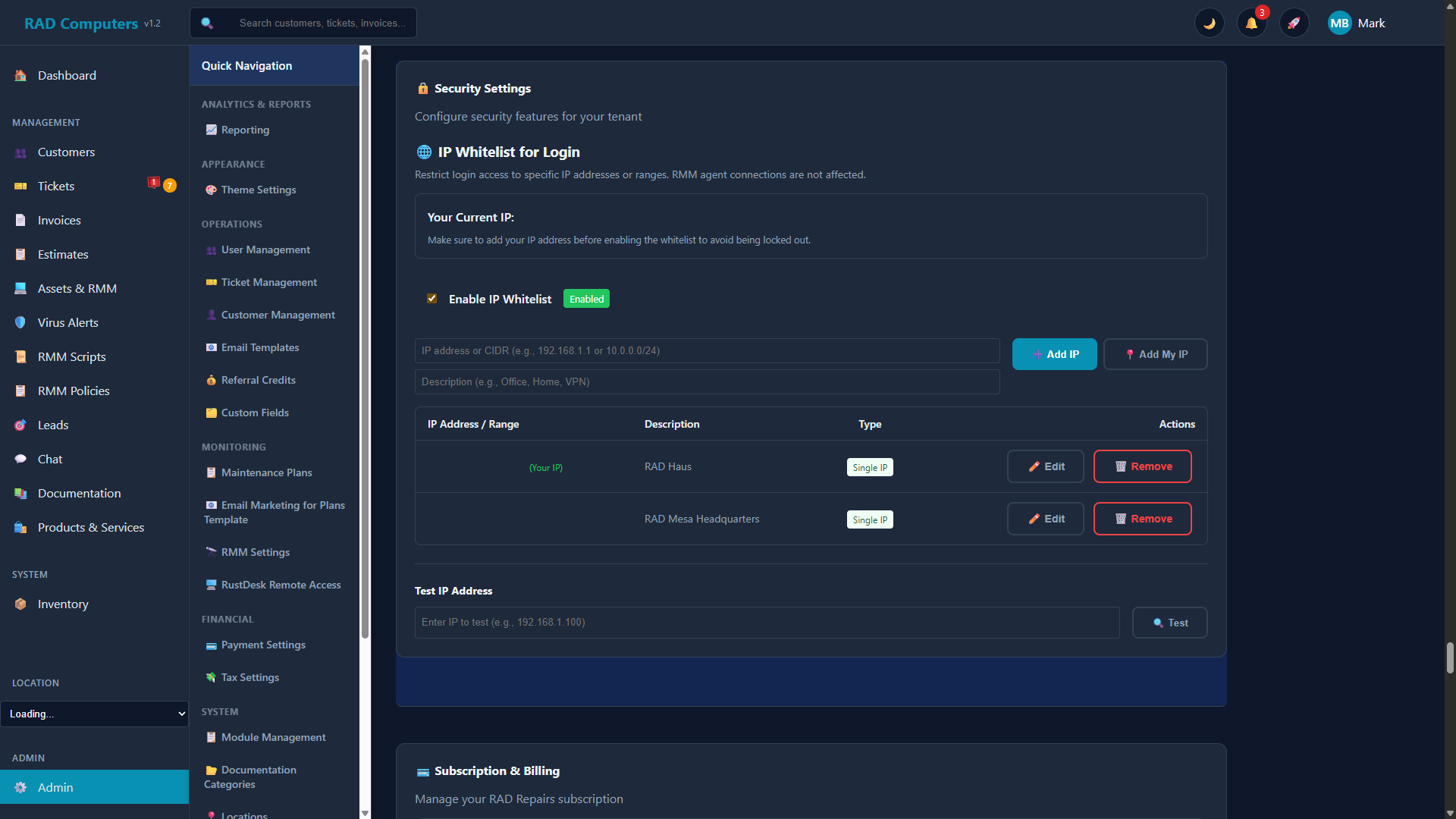
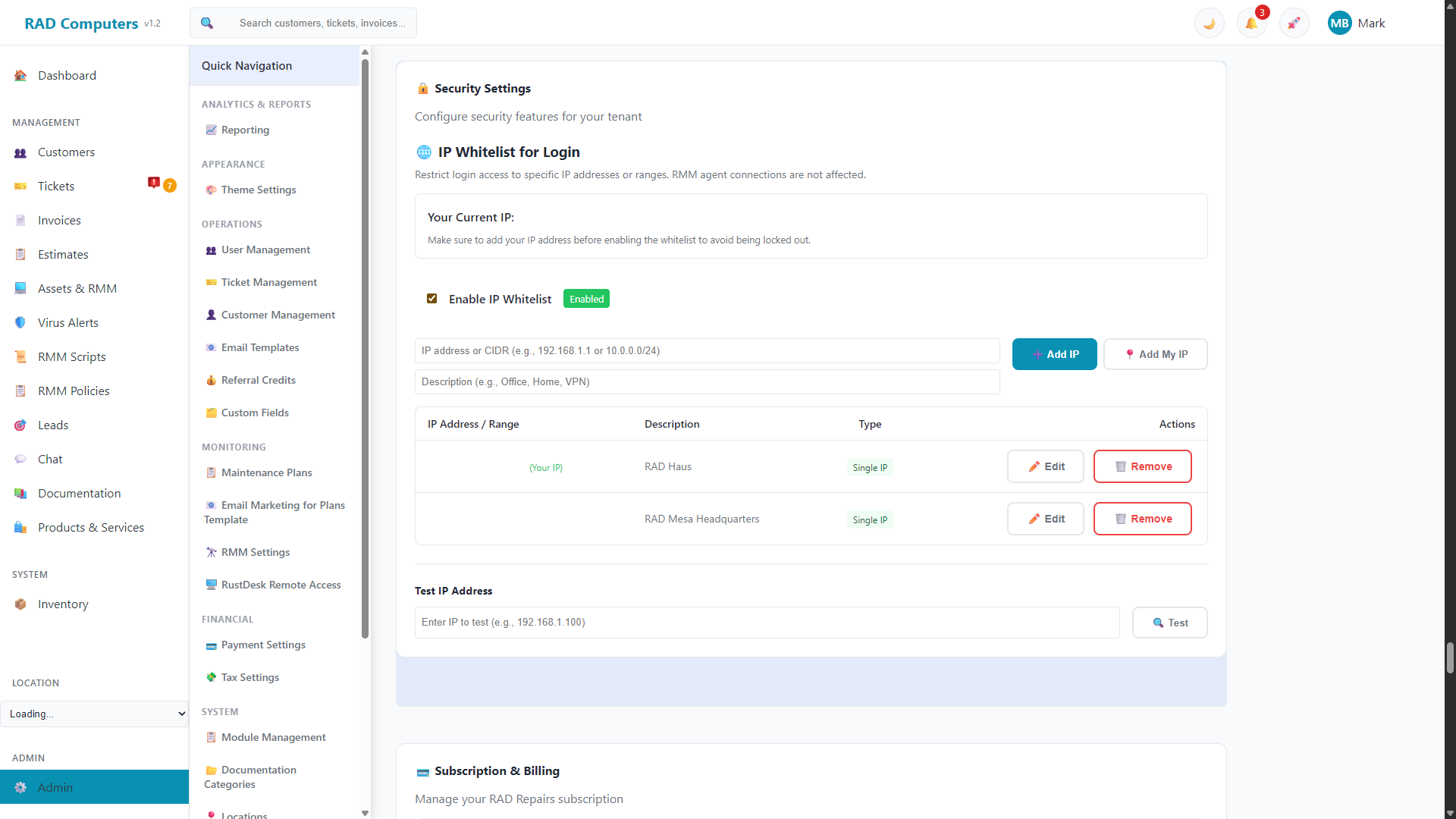
IP Restrictions
For enhanced security, you can restrict access to RAD Repairs based on IP addresses. This is particularly useful for businesses with static IP addresses.
Allowlist Mode
Only allow access from specified IP addresses or ranges:
- Add individual IP addresses (e.g., 192.168.1.100)
- Add IP ranges using CIDR notation (e.g., 192.168.1.0/24)
- Useful for office-only access policies
Blocklist Mode
Block specific IP addresses or ranges while allowing all others:
- Block known malicious IP addresses
- Block entire geographic regions if needed
- Automatically block IPs after repeated failed login attempts
Caution: Be careful when configuring IP restrictions. Incorrect settings could lock yourself or your team out of the application. Always ensure you have a backup access method before enabling strict IP restrictions.
Audit Logging
RAD Repairs maintains comprehensive audit logs of all security-related events. These logs are essential for compliance, troubleshooting, and security investigations.
Events Logged
- Authentication Events - Successful and failed login attempts, logouts, password changes
- User Management - User creation, deletion, role changes, permission modifications
- Security Settings - Changes to security configuration, 2FA enablement/disablement
- Data Access - Access to sensitive records, exports, and bulk operations
- API Activity - API key creation, usage, and revocation
Viewing Audit Logs
Access audit logs from Admin Settings > Security > Audit Log. You can:
- Filter by date range, user, event type, or IP address
- Export logs in CSV or JSON format for external analysis
- Set up automated alerts for suspicious activity patterns
- Configure log retention periods (default: 90 days)
Frequently Asked Questions
What happens if I lose access to my authenticator app?
Use one of your backup codes to log in, then disable and re-enable 2FA to set up a new authenticator. If you don't have backup codes, contact your administrator to temporarily disable 2FA on your account.
Can I use SMS-based 2FA instead of an authenticator app?
RAD Repairs currently supports authenticator app-based 2FA only. SMS-based 2FA is not available due to security vulnerabilities associated with SMS (SIM swapping attacks, SMS interception).
How do I know if someone tried to access my account?
Check your login history in your profile settings, or view the audit log (administrators only). You'll see all login attempts, including failed ones, with timestamps and IP addresses.
Can I set different password policies for different user roles?
Currently, password policies apply to all users equally. However, you can require 2FA only for administrator accounts while making it optional for other users.
How long are audit logs retained?
By default, audit logs are retained for 90 days. This can be configured in Security Settings. For compliance purposes, you may want to extend retention or export logs regularly for long-term storage.
What should I do if I suspect a security breach?
Immediately: 1) Force logout all sessions from your account, 2) Change your password, 3) Review audit logs for suspicious activity, 4) Contact RAD Repairs support if needed. For serious incidents, consider contacting your IT security team or authorities.
Need Help with Security Configuration?
If you have questions about security settings or need assistance configuring your account protection, our support team is here to help.
Contact Support